I was preparing for my company Level seminar on ColdFusion Security this week and gone through numerous blog and slides to learn about recent ColdFusion attacks.
The one which brings me more Interest is IIS Malware attack.
What is it ?
How IIS malware injected in your server ?
Lot's of questions to be asked but the reason for such attack was CF Backdoor Vulnerability.
Yes, If you keep your Door open some one will come and steal some data from your Server.
Here Door terms your ColdFusion Server.
Lets check this IIS Malware Injection through flow chart.
CF vulnerability allowing to create a Web Shell (A Web shell is a type of Remote Access Tool (RAT) or backdoor Trojan file) in server which in turns execute DLL and adds that module in IIS.
Injected DLL was capturing the post request for specific page example paymentProcess.cfm (Installer added this page during installing DLL) and writing POST parameters info in some log file.
Specifically design DLL was also undetectable by modern Anti-Virus.
Even SSL can't stop this. As it captures data after SSL post is decrypted by the server.
It says that how much Imp was to read ColdFusion Lock Down guide. If you have locked your server then well and good. If not then check lock down guides and lock your server soon.
If you are not aware of CF lock down guide please visit :
http://www.adobe.com/content/dam/Adobe/en/products/coldfusion/pdfs/cf10/cf10-lockdown-guide.pdf
I will be coming with next blog which will contain detail recent CF Vulnerabilities.
Hope it may help
The one which brings me more Interest is IIS Malware attack.
What is it ?
How IIS malware injected in your server ?
Lot's of questions to be asked but the reason for such attack was CF Backdoor Vulnerability.
Yes, If you keep your Door open some one will come and steal some data from your Server.
Here Door terms your ColdFusion Server.
Lets check this IIS Malware Injection through flow chart.
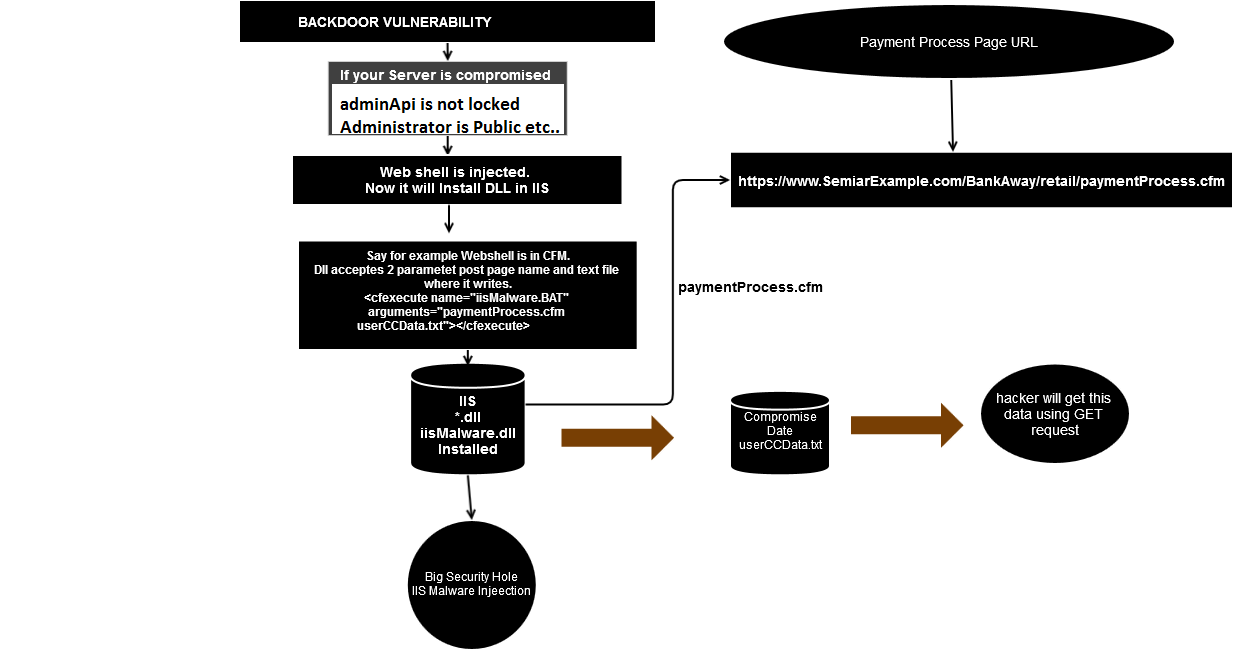 | ||||
| Flow Chart of IIS Malware Injection though CF Backdoor Vulnerability |
Injected DLL was capturing the post request for specific page example paymentProcess.cfm (Installer added this page during installing DLL) and writing POST parameters info in some log file.
Specifically design DLL was also undetectable by modern Anti-Virus.
Even SSL can't stop this. As it captures data after SSL post is decrypted by the server.
It says that how much Imp was to read ColdFusion Lock Down guide. If you have locked your server then well and good. If not then check lock down guides and lock your server soon.
If you are not aware of CF lock down guide please visit :
http://www.adobe.com/content/dam/Adobe/en/products/coldfusion/pdfs/cf10/cf10-lockdown-guide.pdf
I will be coming with next blog which will contain detail recent CF Vulnerabilities.
Hope it may help
No comments:
Post a Comment